The main contract is called Chainpals Token. The minting and transfer of the complete supply is done during deployment. This means new tokens can only be minted if the old ones are burnt.
Deus DAO, a platform offering a framework for optimistic on-chain digital derivatives, has experienced its third major hack across multiple chains, including Arbitrum, BSC, and Ethereum. The recent security breach resulted in token holders losing approximately $6.5 Million, and the DEI stablecoin depegging by over 80%. This event brings into question the trustworthiness of the thrice-hacked protocol, raising concerns for users and investors alike. Despite being a major player in the DeFi space, Deus DAO's continuous security issues highlight the importance of robust smart contract audits and monitoring systems.
The Deus DAO hack had significant financial consequences, with users collectively losing around $6.5 million across Arbitrum, BSC, and Ethereum chains. Furthermore, the hack caused the DEI stablecoin to depeg by more than 80%, destabilizing its value and potentially shaking investor confidence.
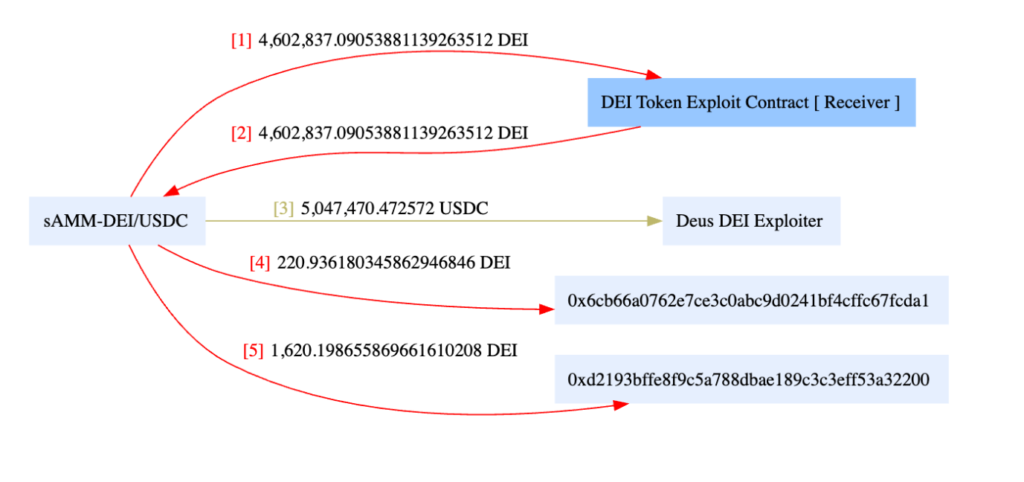
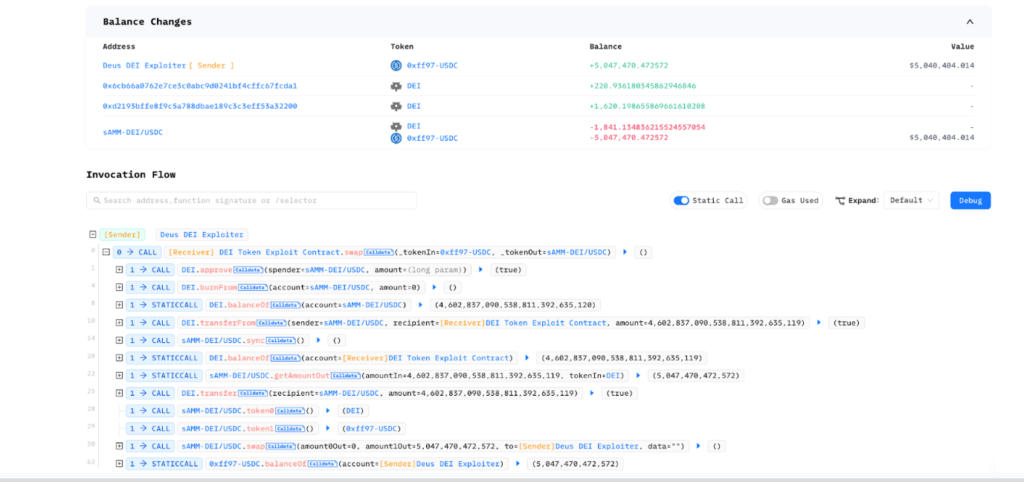
The vulnerability stemmed from a simple implementation error in the DEI token contract that was introduced during an upgrade last month. This error allowed the attacker to manipulate DEI holders' approvals and transfer assets directly to their own address. The losses were approximately $5 million on Arbitrum, $1.3 million on BSC, and $135k on Ethereum. Although some whitehat hackers have managed to return over $600k in USDC to a recovery multisig, doubts remain about the effectiveness of returning funds to a team responsible for such a trivial bug.
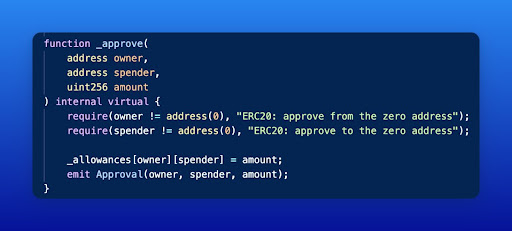
The approve() function is used in ERC20 token contracts to allow one account (the spender) to spend a certain amount of tokens on behalf of another account (the owner). The mapping _allowances[owner][spender] is used to store the approved amount of tokens for a specific owner-spender pair.
Imagine the approve() function as allowing someone to take a certain amount of candies from your candy jar.
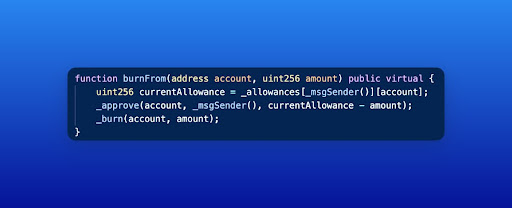
The burnFrom() function is responsible for burning a specified amount of tokens from a given account. In this case, the function reads the allowances mapping to ensure that the spender has enough allowance to burn the tokens from the owner's account. However, there is a critical issue within the burnFrom() function.
The order of the mapping parameters has been flipped, causing it to read from _allowances[attacker][victim] instead of _allowances[owner][spender]. This flipped mapping order allows the attacker to manipulate the allowances and eventually gain control of the victim's tokens.
The attacker first identifies a victim account with a large amount of DEI tokens.
The attacker approves the victim's account for a large amount of tokens using the approve() function. This is like giving someone permission to take a large amount of candies from your candy jar.
The attacker calls the burnFrom() function with the victim's address as the account and 0 as the amount. The flipped mapping order causes the allowances to get updated incorrectly, as the smart contract reads _allowances[_msgSender()][account] instead of _allowances[account][_msgSender()]. Due to this, the contract believes that the attacker has control over the victim's withdrawal limit (allowance).
Inside the burnFrom() function, the _approve() function is called again with the remaining allowance value (currentAllowance - amount). However, due to the flipped order, the allowance mapping is now set as _allowances[victim][attacker]. This means that the victim's account has given the attacker an allowance to spend a large amount of tokens from their account, just like mistakenly giving someone permission to empty your entire candy jar.
Now that the attacker has been granted a large allowance from the victim's account, they can call the transferFrom() function to transfer the victim's tokens to their own account. The smart contract believes the attacker has the right to do so and allows the transfer, resulting in the theft of the victim's funds.
Arbitrum: 0x189cf534de3097c08b6beaf6eb2b9179dab122d1
BSC: 0x5a647e376d3835b8f941c143af3eb3ddf286c474
Ethereum: 0x189cf534de3097c08b6beaf6eb2b9179dab122d1
These are the addresses used by the attacker to execute the hack on different blockchains and receive the stolen DEI tokens. By examining the transaction history of these addresses, we can trace the steps taken by the attacker, including the preparation for the attack and the subsequent token transfers.
Arbitrum: 0xb1141785...
BSC: 0xde2c8718...
Ethereum: 0x6129dd42...
These transactions showcase how the attacker exploited the vulnerability in the DEUS DAO smart contract to steal DEI tokens. By analyzing these transactions, we can observe how the attacker manipulated the approve() and burnFrom() functions.
The DEUS DAO hack highlights the importance of thorough security measures when developing and deploying smart contracts in the decentralized finance ecosystem. This particular exploit was a result of a simple yet critical vulnerability in the burnFrom() functions, which enabled the attacker to manipulate allowances and steal millions of dollars worth of DEI tokens from unsuspecting users.
As DeFi platforms continue to grow in popularity, it is crucial for developers and project teams to prioritize the security of their smart contracts and to learn from incidents like the DEUS DAO hack. Implementing strong technical mitigations, conducting comprehensive audits, and engaging the community can significantly reduce the risk of security breaches and ensure a safer environment for users.
In light of this incident, we strongly recommend projects to get their smart contracts audited by reputable security firms such as BlockApex.io. A thorough audit conducted by experienced professionals can help identify and address vulnerabilities before they can be exploited by malicious actors, ultimately safeguarding the integrity of the platform and its users' assets.
By taking these important steps, DeFi platforms can continue to innovate and thrive while ensuring the security and trust of their users.

The main contract is called Chainpals Token. The minting and transfer of the complete supply is done during deployment. This means new tokens can only be minted if the old ones are burnt.
Over $720M worth of funds were stolen this month, illuminating a dangerous message about the security and reliability of these platforms- raising several questions. Is orchestrating an attack of this level really so easy? If I happen to be a daring individual with the right technical skills, can I too be the owner of millions of dollars worth of funds? And most importantly, what measures can other platforms take beforehand to ensure they and their users are safe from becoming the next target?
Jimbo's Protocol is a decentralized finance (DeFi) system built on the Arbitrum chain. The protocol uses a semi-stable floor price for its ERC-20 token, $JIMBO, backed by a treasury of Ether (ETH). However, despite its pioneering efforts to maintain on-chain liquidity and price floors, Jimbo's Protocol recently faced a Flash loan attack.
In April 2023, Merlin DEX,a decentralized exchange (DEX) built on ZkSync, suffered a hack during a Liquidity Generation Event for its MAGE token, resulting in an estimated loss of $1.8 million from the protocol.
In a world where personal data has become more or less a commodity, the potential advantages provided by zero-knowledge proofs are monumental. By combining them with blockchain technology, a powerful mix of immutability and security can be achieved.
The AI and blockchain integration can help overcome some of the limitations of each technology and create a more secure, transparent, and efficient Web3 ecosystem. This article explores the differences between AI and blockchain, ways to integrate them, use cases, and challenges that need to be addressed.
Rari capital got hacked for around $79M through a classic re-entrancy attack. Rari is a fork of compound finance which had this bug fixed earlier. It is not the first time Rari has been a victim of a hack.
The Yearn Finance hack that occurred on April 13, 2023, resulted in the loss of approximately $11.4 million. The exploit was carried out through a misconfiguration in the yUSDT vault, revealing a flaw in the system's architecture.
The dual nature of Tornado Cash brings forth layers of doubt surrounding its morality. Who benefits more from using Tornado Cash? The average man concerned about his privacy, or a criminal with millions of dollars worth of stolen funds?


