how do we keep the blockchain application safe? Let's walk through some security frameworks for blockchain applications in this blog
On Tuesday, 9th August, Curve Finance suffered from a DNS attack causing theft of a whooping $570,000+ USD.
Curve Finance is a stablecoin decentralized exchange (DEX) that runs on the Ethereum blockchain.
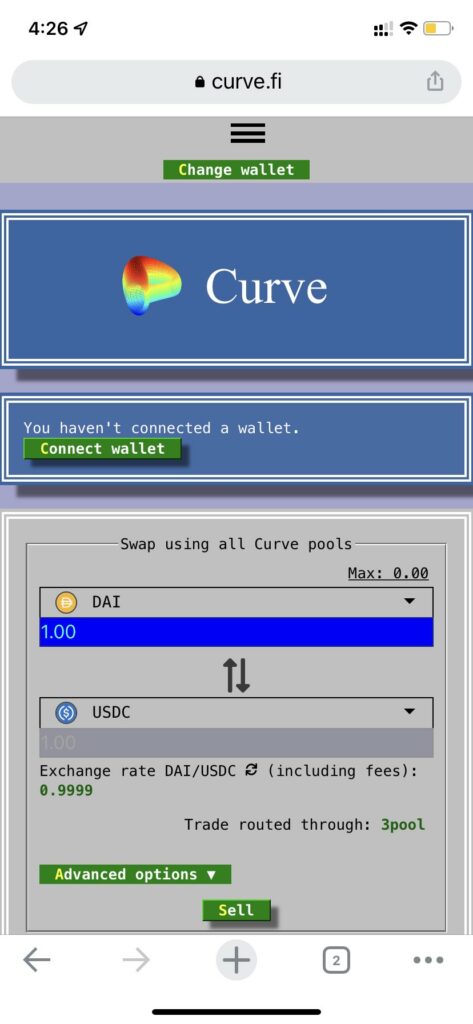
The attacker targeted the front end where the suspected hacker appears to have changed the domain name system (DNS) entry for the protocol, forwarding users to a fake clone website and approving a malicious contract. The program’s contract remained uncompromised, however.
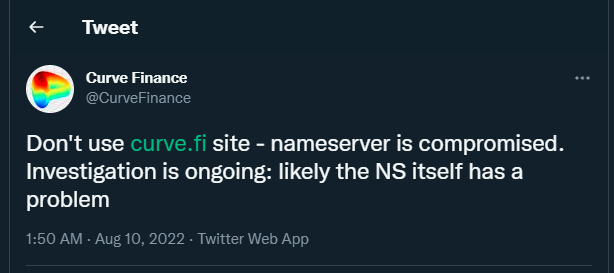
The team behind the protocol noticed the issue and tweeted to warn the users about the exploit.
A few hours after the exploit Curve again tweeted confirming both that they have found the issue and also reverted it. They also asked the user to immediately revert any contract they have approved on Curve prior.
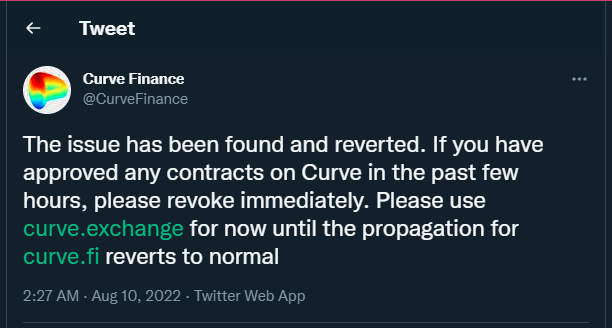
Curve explained that it was most likely that the DNS server provider Iwantmyname was hijacked. On the other hand, the exploit was going on, Twitter user LefterisJP speculated that the alleged attacker had likely utilized DNS spoofing to execute the exploit on the service.
Other users quickly noticed and tweeted to warn the users that the alleged thief appears to have stolen more than $573,000 USD.


how do we keep the blockchain application safe? Let's walk through some security frameworks for blockchain applications in this blog
This blog explores the fascinating world of fuzz testing methodologies and frameworks. We delve into stateless and stateful fuzzing. Bounded Model Checking (BMC) is introduced as a technique to verify systems against predefined specifications. Additionally, we discuss the essence of End-to-End (E2E) testing, combining structured scenarios with fuzz testing's unpredictability. Lastly, we compare renowned fuzzing tools, Echidna and Foundry, highlighting their unique features and differences.
Flower Fam is an NFT-based project, after you mint your NFT you can “harvest” them on weekly bases to get 60% royalties. It's quite simple: every flower has a 10% chance to win. The rarer the species of a flower.
Safemoon suffered an attack in which the SFM/BNB pool was drained, resulting in a loss of $8.9M worth of ‘locked LP’. The attack was carried out by exploiting a vulnerability in the new Safemoon contract that allowed anyone to burn SFM tokens from any address, thus inflating the price of SFM tokens in the pool.
Consensus algorithms are undoubtedly a major building block of blockchain technology. By definition, no single party can control the operation of a blockchain network, so consensus algorithms are relied on to achieve a common agreement.
The attack on dForce network had significant consequences for the platform and its users. By exploiting a reentrancy vulnerability in the wstETH/ETH pool on Curve and the dForce wstETH/ETH Vault, the attacker was able to manipulate the virtual price of the pool, which in turn affected the oracle used by the dForce wstETH/ETH Vault
On April 15th, 2023, Hundred Finance was hacked, resulting in a loss of approximately $7.4 million USD in various cryptocurrencies. The attacker exploited an integer rounding vulnerability in the platform's contract logic when a market was empty.
The SEC describes its motives to be the safeguarding of investors, while members of the blockchain community see their actions as sabotage. Read more to find out the history of this controversy and its implications on the general definition of security.
Yamato Protocol is a crypto-secured stablecoin generator DApp pegged to JPY. Yamato Protocol is a lending decentralized financial application (DeFi) that can generate Japanese Yen stablecoin "CJPY". It is being developed by DeFiGeek Community Japan, a decentralized autonomous organization.


