It is crucial to come up with innovative solutions against cyberattacks, especially when your workforce is remotely working. Since we know that remote work comes with a bunch of security risks, it is essential to cater to them.
Written in May 2023
In the emerging realm of DeFi, Merlin DEX stands as a novel, community-centric Decentralized Exchange (DEX) built on ZkSync, aiming to tackle the persistent "liquidity problem". By creating a robust liquidity environment, Merlin is paving the way for more efficient and accessible liquidity solutions.
Pushing the limits of Automatic Market Makers (AMMs), Merlin DEX has developed a unique mechanism to focus liquidity around target prices, optimizing speed, reliability, and reducing fees.
Merlin DEX's strong commitment to decentralization and its unique approach to Liquidity Generation Events (LGEs) stands as a testament to its innovative vision. Allowing users more control and transparency, Merlin is dedicated to creating an open, borderless DeFi environment.
In April 2023, the Merlin DEX unfortunately fell victim to a hack, resulting in an estimated loss of $1.8 million from the protocol. The hack occurred amidst a Liquidity Generation Event for the launch of its MAGE token.
The attacker exploited excessive permissions granted to the Feeto address used during deployment, enabling them to drain the pool of assets. This event highlights the potential risks of overly centralized control in a DeFi protocol and emphasizes the importance of implementing decentralization best practices.
The pool creator (address: 0xc0D6987d10430292A3ca994dd7A31E461eb28182) created a Factory Contract (0x63E6fdAdb86Ea26f917496bEEEAEa4efb319229F). In the process, the creator set the Feeto address, which is meant to collect transaction fees, to their own address. This essentially means the creator holds excessive control over the protocol.
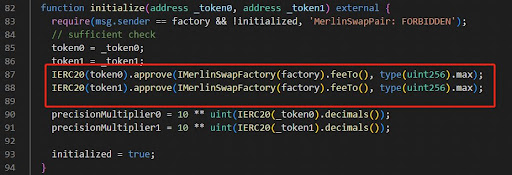
Next, a USDC-WETH pool was deployed using the Factory Contract. During initialization, the pool’s USDC and WETH tokens were given max approval to the Feeto address of the factory contract. This is risky because whoever controls the Feeto address can move all the tokens from the pool.
Leveraging this excessive permission granted to the Feeto address, the attacker (same as the pool creator in this case) transferred all tokens from the pool to their own address.
Interestingly, the owner and Feeto addresses of the Factory Contract had been changed before the attack. While this step was not necessary to execute the hack, it served to confuse observers and potentially divert attention away from the real exploit.
To simplify, imagine the Factory Contract as a vending machine factory and the pool as a vending machine. The vending machine factory was set up such that all vending machines it produces would give all the money inside them to the factory owner. The attacker created a vending machine (pool), which was programmed to give all its money to the factory owner, and took all the money out of it. Then, to confuse people, they changed the owner of the factory, even though it had nothing to do with their ability to empty the vending machine.
Permissions should be the least required to fulfill functionality. If a contract or a particular address doesn't need the ability to move all tokens, it shouldn't have that power. Always implement "principle of least privilege."
Continuously monitor contract activity, especially for contracts holding substantial value. Rapid detection and response can mitigate damage if an attack happens.
If possible, using multi-signature wallets for critical operations or ownership changes could provide an additional layer of security. This requires multiple people to agree on a transaction before it's processed.
Transparency in code helps the community to verify the contract's operation and provides an additional layer of security through community auditing.
For crucial contract functions, consider implementing time locks. Time locks require a waiting period before certain functions can be executed, giving the community time to react if something appears malicious.
Implement an emergency shutdown or pause mechanism to stop contract operations in case of detection of malicious activities.
The factory contract was created by the pool creator (0xc0D6987d10430292A3ca994dd7A31E461eb28182). This contract is where the USDC-WETH pool was deployed from. During initialization, the Feeto address was set to be the same as the creator's address, presenting a centralization risk.
This is the Ethereum address of the individual or entity who deployed the factory contract and the USDC-WETH pool. They initially had control over the Feeto address, which was later changed, presumably to avoid suspicion or confuse investigators.
This pool was created through the factory contract and granted maximum approval to the Feeto address of the factory contract. Essentially, the Feeto address had complete control over the funds within this pool, leading to the theft.
This incident demonstrates the critical importance of secure smart contract design and the necessity of rigorous auditing. The attack on the Merlin DEX on ZkSync, which resulted in a loss of $1.8M, exploited the centralization of power in the factory contract's Feeto address, leading to the unauthorized transfer of tokens from the USDC-WETH pool.
A comprehensive security audit, such as those provided by BlockApex, can greatly enhance the security posture of a DeFi protocol. Such audits can identify and address vulnerabilities before they are exploited, protecting users and ensuring the sustainable growth of the protocol. Smart contract audits are a key defensive measure, and their importance cannot be overstated in the rapidly evolving and highly competitive DeFi landscape.

It is crucial to come up with innovative solutions against cyberattacks, especially when your workforce is remotely working. Since we know that remote work comes with a bunch of security risks, it is essential to cater to them.
Vaccify is an open-source COVID-19 Initiative of TrustNet. The idea behind it is to issue digital certificates to people who are vaccinated (once the vaccine is available) for COVID-19. It is a Blockchain-based digital identity eco-system for all hospitals, healthcare centers, laboratories, and testing facilities across Pakistan.
The attack on dForce network had significant consequences for the platform and its users. By exploiting a reentrancy vulnerability in the wstETH/ETH pool on Curve and the dForce wstETH/ETH Vault, the attacker was able to manipulate the virtual price of the pool, which in turn affected the oracle used by the dForce wstETH/ETH Vault
On April 15th, 2023, Hundred Finance was hacked, resulting in a loss of approximately $7.4 million USD in various cryptocurrencies. The attacker exploited an integer rounding vulnerability in the platform's contract logic when a market was empty.
The purple team exercises allow for regular testing of controls to ensure they still function as expected. Combining red and blue functions also means that the blue team does not have to learn the red-team skills, or take the time to recreate attack behaviors themselves.
Data breaches and consumer privacy are one of the most alarming security issues in IT space. About 45% of the world’s population uses social media which makes approximately 3.48 billion people to be interacting with any kind of social media network. These tremendous amounts of connections can lead to various kinds of vulnerabilities if the data is gone into the wrong hands creating pretty damaging consequences.
BlockApex conducted smart contract audit for Dafi v2 protocol. This document presents the findings of our analysis which took place from 16th Dec 2021 to 14th Jan 2022.
Learn how Fuzz Driven Development (FDD) transforms software testing by assisting programmers and testers in overcoming prejudices for improved code quality, security, and performance.
On February 17, 2023, Platypus Finance was hacked, resulting in a loss of approximately $8.5 million worth of assets. In this hack analysis, we will delve into the details of the attack, the vulnerability that was exploited, and the impact it had on the platform and its users.


